In the fast-evolving world of Web3, Solana stands out for its high throughput and low costs, making it a prime choice for gated communities and allowlists. Yet, as projects scale, ensuring KYC verification allowlists Web3 without sacrificing user privacy has become a pressing challenge. Enter onchain KYC attestations Solana, a breakthrough that lets users prove compliance through signed, verifiable credentials tied to their wallets. No more repeated verifications or data honeypots; instead, reusable proofs that respect sovereignty while meeting regulatory needs. By early 2026, this infrastructure has matured, powering Solana gated communities attestations with elegance and efficiency.
Solana Attestation Service: The Backbone of Privacy-Preserving KYC
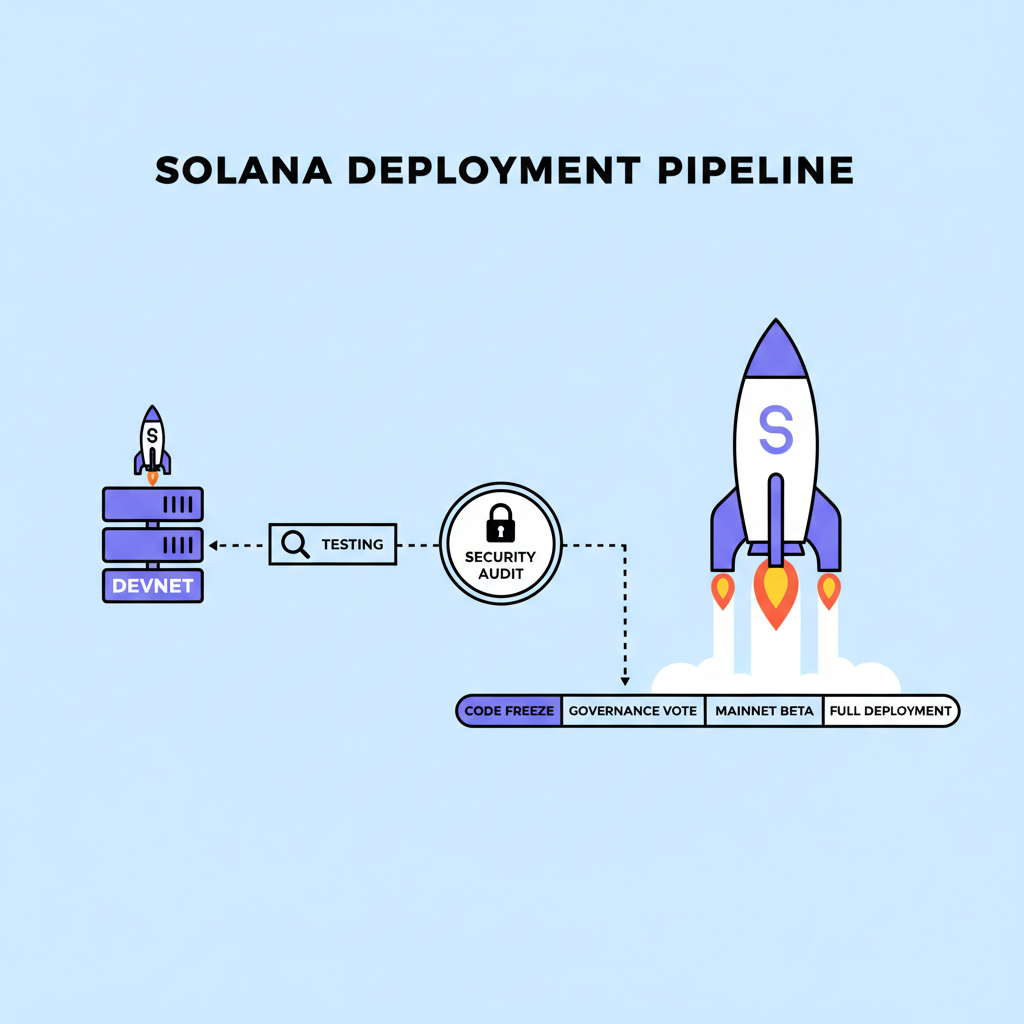
Launched in May 2025, the Solana Attestation Service (SAS) marks a pivotal shift in how blockchains handle identity. This permissionless protocol allows trusted issuers, like verification providers, to link off-chain KYC data to on-chain accounts. Attestations are cryptographically signed, ensuring tamper-proof verifiability across dApps. Crucially, sensitive details stay off-chain; users share only what's necessary via selective disclosure. I see SAS as a game-changer because it eliminates the KYC bottleneck that has plagued DeFi and token launches for years.
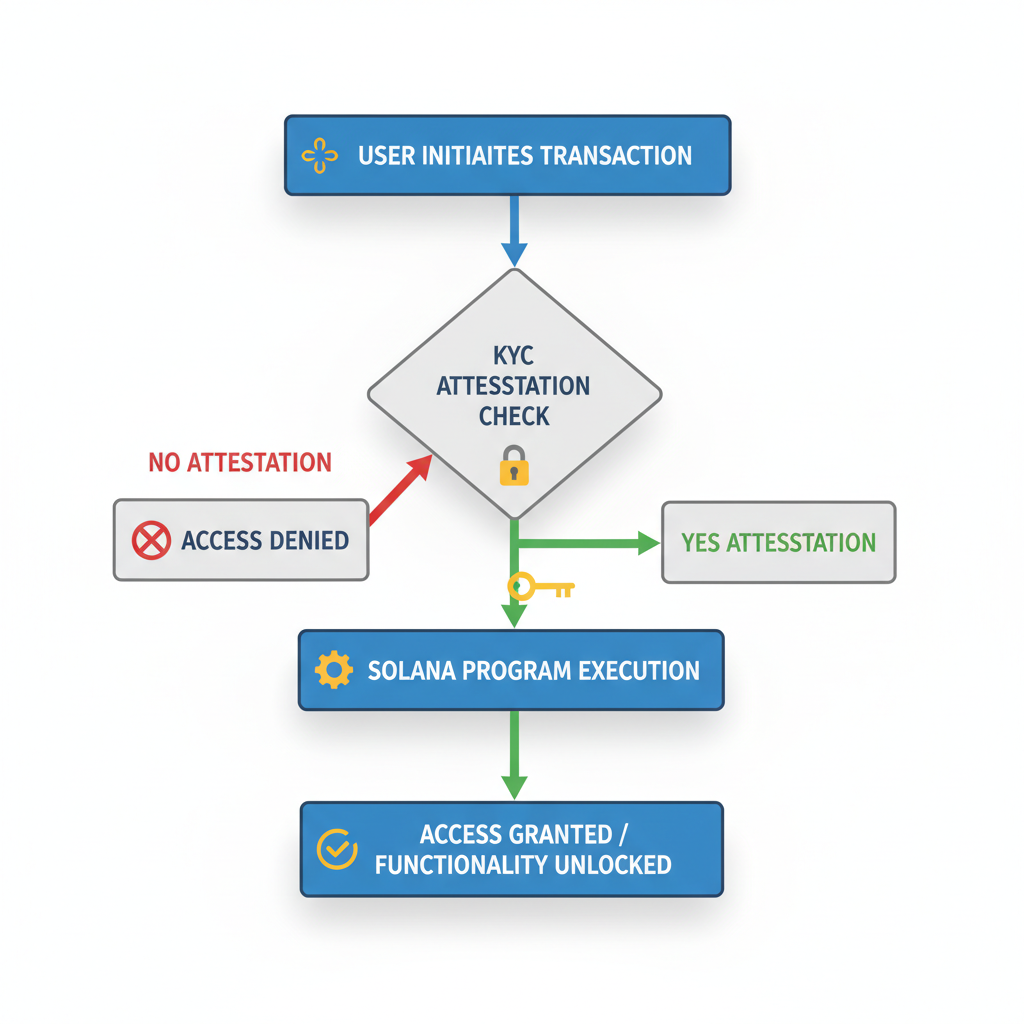
Projects can gate access to allowlists by checking for a valid SAS attestation, confirming KYC status without exposing personal info. This aligns perfectly with Solana's ethos of speed and scalability, where verifications settle in seconds at minimal cost. For allowlist managers, it means streamlined operations: one verification, endless reusability.

Take zkSign, a complementary tool introducing zero-knowledge proofs to Solana. Users prove criteria like "KYCed in jurisdiction X" without revealing their full identity. This layer adds robust privacy preserving KYC blockchain mechanics, vital for global projects navigating diverse regulations.
Real-World Integrations Driving Adoption
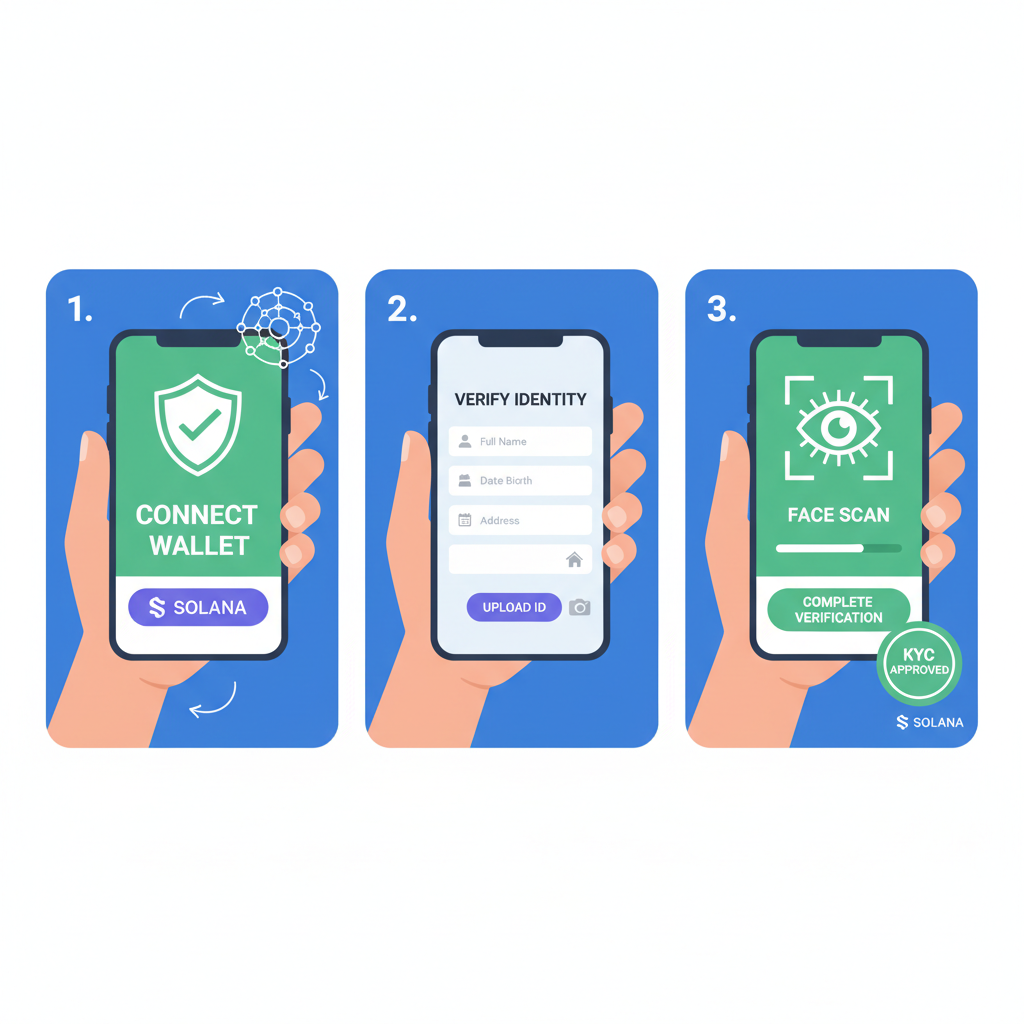
Sumsub's May 2025 integration with SAS exemplifies practical impact. This global verifier now issues on-chain identity proofs directly to self-custodial wallets. Users carry these "digital passports, " verifiable publicly yet private in essence. For Solana allowlists, this means instant compliance checks during token sales or community access, reducing friction dramatically.
The January 2026 Privacy Hackathon further accelerated momentum. With over $100,000 in prizes, developers built tools for private payments and identity solutions, many leveraging SAS for onchain attestations. Winners showcased applications like reputation-based gating, where users accumulate credentials over time.
Solid Labs pushes boundaries with decentralized identity primitives on Solana. Users mint unique on-chain identities, collecting attestations for KYC, social proof, and more. This composability fosters trustless exchanges, ideal for onchain identity Solana 2026. Range's integration enriches wallet intelligence by parsing these attestations, aiding security teams in risk assessment without invasive data grabs.
Building Resilient Allowlists with Reusable Credentials
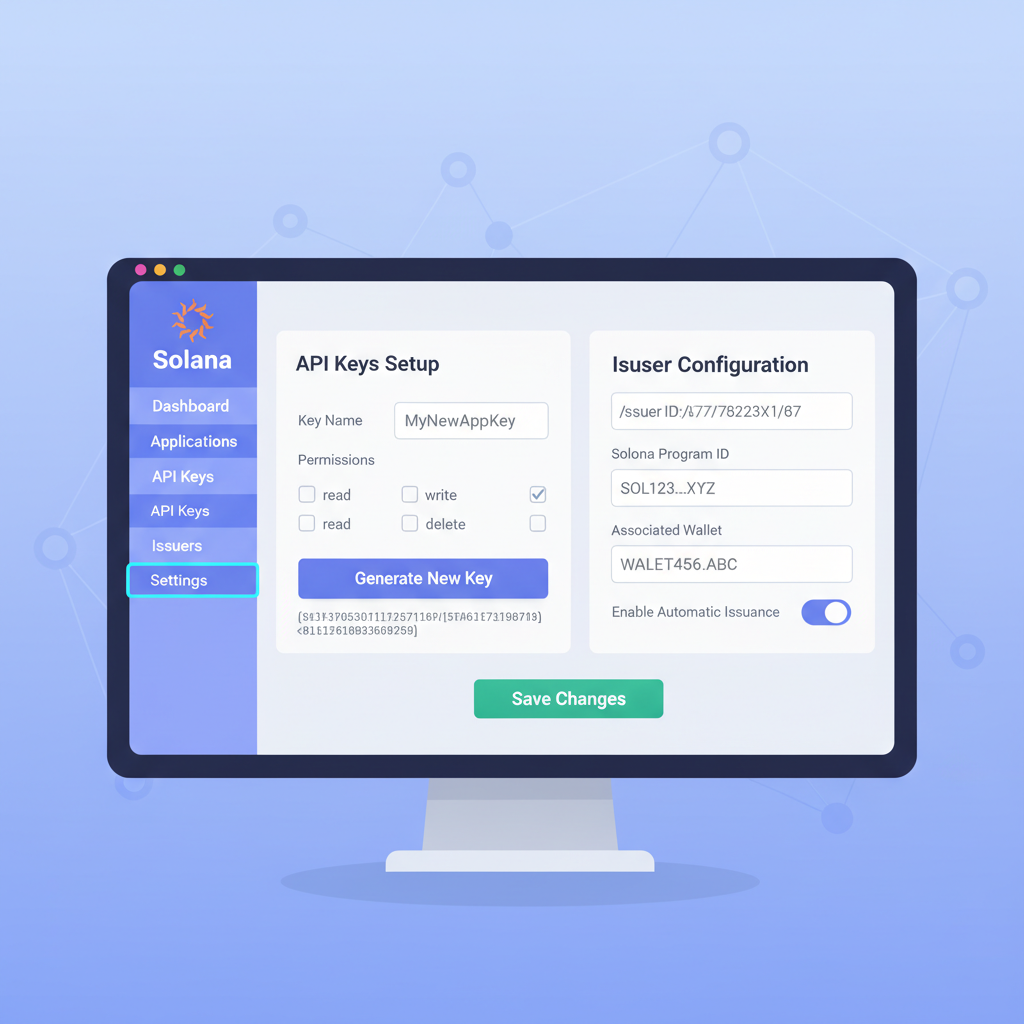
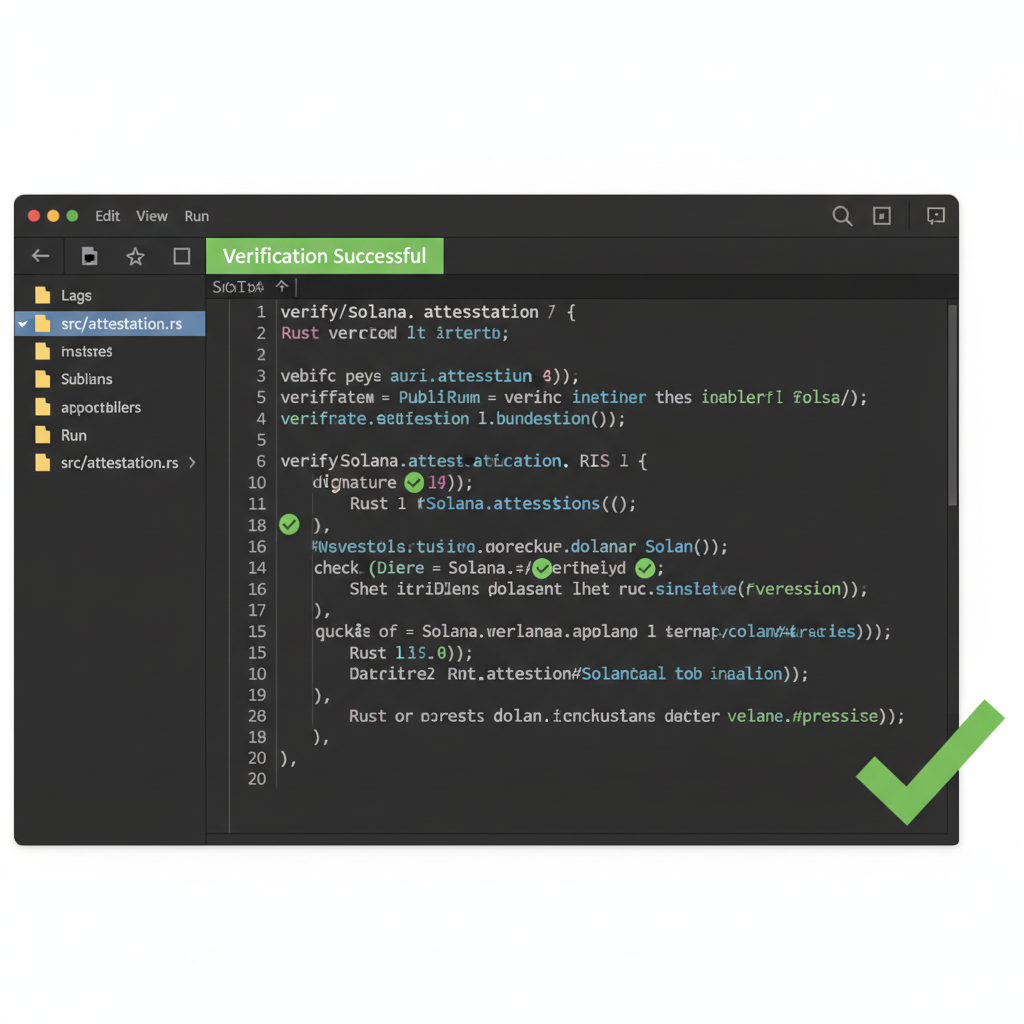
Imagine a DeFi protocol launching an airdrop exclusive to verified addresses. Traditionally, this invites sybil attacks or compliance headaches. With SAS, issuers like OnchainKYCe. me provide attestations that projects query on-chain. A simple program derives instruction checks if the wallet holds a valid KYC credential from an approved issuer. No central database, no repeated uploads; just pure, programmable trust.
This model extends to simplifying KYC for DeFi airdrops and allowlists, where attestations enable permissionless yet secure participation. Multi-issuer support adds flexibility: a user KYCed via Sumsub can reuse that proof elsewhere, building a portable reputation. In my view, this user-centric approach will define Web3's mature phase, balancing innovation with accountability.
Developers benefit from SAS's open standard, interoperable with tools like Chainlink oracles for hybrid verifications. Costs? Pennies per attestation, thanks to Solana's efficiency. Early adopters report 90% reductions in verification overhead, proving the economic edge.
Security teams at protocols like Marginfi or Drift have already integrated Range's SAS parsing to flag high-risk wallets dynamically, all while users retain control over their data. This isn't just theoretical; it's reshaping how Solana projects handle onchain identity Solana 2026.
Step-by-Step: Issuing and Verifying KYC Attestations for Allowlists
Once issuers like OnchainKYCe. me or Sumsub complete the off-chain check, they publish the attestation on-chain. Developers then write Anchor programs to validate these at runtime. For instance, during an allowlist mint, the instruction queries the wallet's attestations, checks issuer trust, expiration, and revocation status. zkSign can wrap this in a ZK proof for even tighter privacy, proving membership without full disclosure.
This workflow scales effortlessly. A project with 100,000 users verifies each in under 400ms, costing fractions of a cent. No more CSV uploads or snapshot services; everything's native and composable. I've advised teams transitioning from centralized KYC providers, and the switch cuts support tickets by half while boosting user retention through frictionless access.
Top Advantages for Solana Gated Communities
Key benefits of onchain KYC attestations for Solana allowlists
| Benefit | Short Description | |
|---|---|---|
| Reusable Credentials | 🔄 | Verified once, proof reusable indefinitely across platforms |
| Selective Disclosure | 🔒 | Reveal only necessary info without over-sharing |
| Multi-Issuer Flexibility | 🌐 | Works with credentials from any trusted issuer |
| Low-Cost Verification | 💰 | Cheap and fast on Solana |
| Sybil Resistance | 🛡️ | Prevents fake accounts and duplicates |
Reusable credentials top the list because they end the verification treadmill. A user KYCed once carries proof indefinitely, revocable only by the issuer. Selective disclosure lets them reveal just "over-18" or "non-sanctioned, " aligning with data minimization principles. Multi-issuer setups build ecosystems of trust; if Sumsub vouches for you, Jup. ag or Backpack can accept it too.
Sybil resistance shines in airdrops and DAOs. Attackers can't spin up fake wallets en masse when each needs a real-world tie. Costs stay negligible, unlike Ethereum's gas wars for similar proofs. For Solana gated communities attestations, this means vibrant, compliant spaces without gatekeeping vibes.
Challenges persist, sure. Issuer collusion risks exist, so projects curate trusted lists transparently. Revocation mechanisms, baked into SAS, mitigate this by allowing instant invalidation. Regulators appreciate the auditability; every claim traces back immutably. Pair it with Chainlink for oracle-fed compliance data, and you've got a fortress.
Looking ahead, the Privacy Hackathon's crop of tools hints at explosive growth. Expect zk-powered social graphs, where attestations layer reputation atop KYC. Solid Labs' primitives could spawn identity DAOs, letting communities co-own verification schemas. Range's analytics will evolve into predictive risk engines, scanning attestation patterns for anomalies.
For allowlist managers eyeing 2026 launches, start small: integrate SAS for your next token sale via enhancing KYC compliance for DeFi allowlists. Test with zkSign for proofs, monitor via Range. The result? Loyal users who stick around because onboarding feels magical, not bureaucratic.
Onchain KYC attestations aren't a buzzword; they're the plumbing for Web3's compliant golden age. Solana's speed turns this into reality faster than rivals. Projects ignoring it risk obsolescence as users flock to seamless, sovereign identity. Dive in, build boldly, and watch your community thrive on verifiable trust.








No comments yet. Be the first to share your thoughts!